From employee payroll to customer transactions, there are numerous opportunities for hackers to steal your small business’s financial data. However, in the fast-paced business world, there’s no time to waste when handling a data breach.
Unlike larger corporations, your business likely doesn’t have an armory of security tools. However, there are countless, low-cost measures you can take to protect your financial information.
On the other hand, you may think that because your business is smaller, it’s less likely to be attacked. Hackers have bigger fish to fry, right? Wrong. If anything, cybercriminals will target your business because you don’t have the same security tools that corporations do.
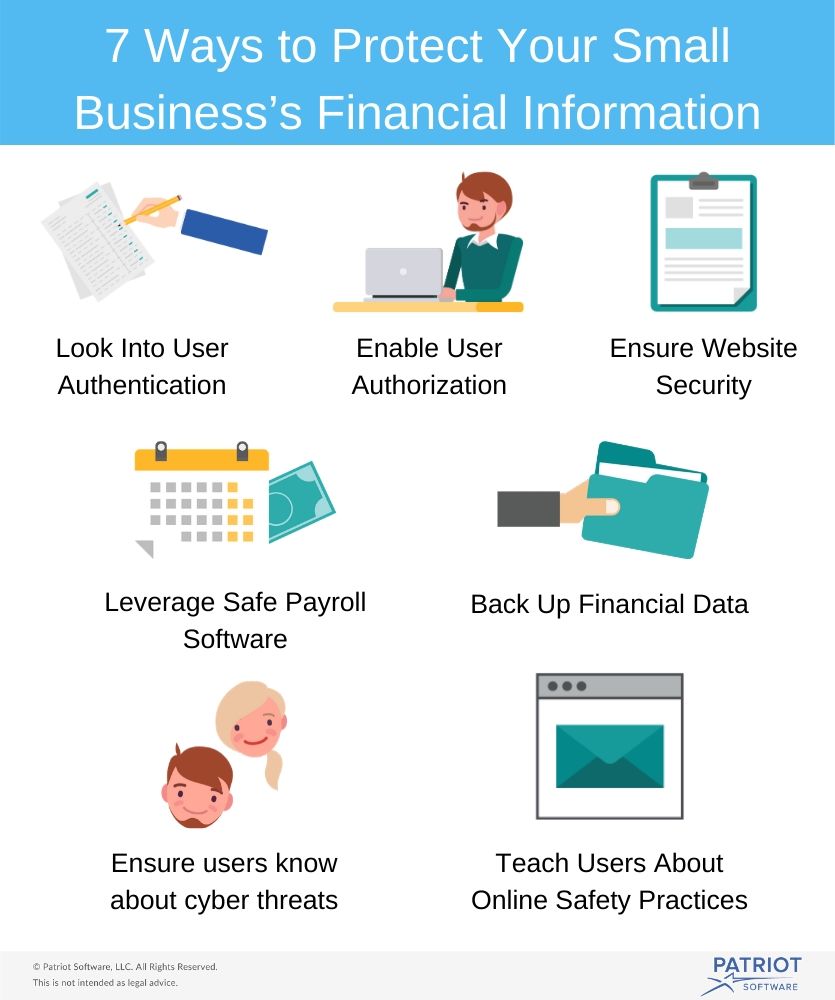
If you’re looking to expand your cybersecurity strategy, here’s what you should do:
- Look into user authentication
- Enable user authorization
- Ensure website security
- Leverage safe payroll software
- Back up financial data
- Teach users about online safety practices
- Ensure users know about cyber threats
Not only will a data breach affect your current employee base, but it will drive away potential candidates and customers, too. Ready to secure your financial information? Let’s get started!
1. Look into user authentication
As a major first step toward a more secure business, enable a user authentication tool. Essentially, user verification lets you know that your users are who they say they are.
The traditional authentication method is simply a username and password, but these days, that’s no longer enough.
As technology continues to advance, so do hacking techniques. To create more barriers between hackers and your financial data, look into the following user authentication types:
- Knowledge factors. These are anything a user must know to log in. This includes traditional login credentials (i.e. username and password) as well as pin numbers and security questions. These tend to be less secure because they can be guessed easily.
- Possession factors. These are anything a user must physically have to log in. For instance, they may need a one-time password token, which is sent by email, by text, or in an authenticator app.
- Inheritance factors. This is when a user must use biometrics to log into their account. For example, fingerprint scanning and face recognition fall under this category.
You may be tempted to implement security questions on top of traditional login credentials and call it quits, thinking that’s enough to deter hackers. However, with a quick search, unauthorized users can easily guess the answers. Make sure you’re implementing the appropriate user authentication steps, preferably those that involve possession or inheritance factors.
2. Enable user authorization
While user authorization may sound strikingly similar to user authentication, they’re two different levels of security. Once a user has been authenticated, their authorization level determines what they have access to. Before you implement either of them, be sure to learn their key differences between security authentication and authorization.
Defining permissions is vital to a safe financial strategy. Here are a couple of reasons for enabling authorization levels:
- They prevent users from accessing other accounts’ information. For instance, you don’t want employees to be able to see anyone’s payroll but their own. Authorization restrictions ensure that users can only access their own private information.
- They restrict employee access to certain elements of a user’s profile. Your marketing team may need a user’s shipping address, but they should never have access to their login credentials or credit card details.
Authorization is just as important as authentication. When you don’t control what users can and can’t see, your financial information is just as unsafe as it would be without the initial authentication layer.
3. Ensure website security
Once you’ve enabled your first line of defense, you’ll need to secure your website. Otherwise, customers won’t feel comfortable sharing their payment data, and employees won’t feel as if their payroll data (such as bank routing numbers) is safe.
If you don’t rely on secure accounting and payroll software, there are a few steps you can take to protect your own data:
- Encrypt your data. Basically, encryption is the process of encoding information in a way where only authorized parties can access it.
- Use tokenization. Tokenization replaces sensitive data with an algorithmically generated number. Then, it stores the actual private data outside of its original environment.
- Invest in SSL certificate authentication. A secure sockets layer (SSL) certificate allows the web server to initiate secure sessions with users. Because you’ll be dealing with financial information, you should use an Extended Validation (EV) SSL certificate.
You can never take too many security precautions. From hosting an eCommerce site to distributing payroll, there are too many chances for mistakes. However, when you implement these extra security layers, you minimize hackers’ opportunities for accessing your financial data.
4. Leverage safe payroll software
As a small business, your team likely doesn’t have time to handle payroll on its own. Plus, implementing extra security measures for accounting can be time-consuming at the start. That’s where cloud payroll software comes into play.
Not only should your system be affordable, dependable, and accurate, it should also be secure. When selecting your provider, check for the following safety features:
- Password protection so no unauthorized users gain access
- Access control to limit who sees what within the system
- Secure storage such as encryption and tokenization
- Timeout to log employees out after periods of inactivity
Before investing, make sure to do ample research. Check to see if payroll providers you’re interested in have a history of data breaches and if their current customers are happy with their security measures. Otherwise, your payroll software may wind up wasting time instead of saving it.
Plus, you should leverage this information when investing in other software, too. For instance, check security features with customer relationship management systems, marketing tools, and so on. After all, technology is intended to speed up your business, not interrupt your workflow.
5. Back up financial data
While you should store your financial information in one central location, you should also back up this data. Better yet, it should be backed up online.
That way, if you forget to update your antivirus software and get hacked, you’ll have a secure backup. If you do get a virus and don’t have a backup, that data will likely be completely unrecoverable.
You should also have a backup stored on an external hard drive. However, avoid transferring this data via USB unless absolutely necessary. Once you’re done backing up data, make sure to disconnect the device as it can be vulnerable to an attack, too.
Access to critical financial information should be limited to as few computers as possible. Remember to never share this information via email, either.
The more you transfer and share this data, the more prone it is to being stolen. In other words, limit your backup locations as a way to secure payroll and other financial data.
6. Teach users about online safety practices
There’s only so much you can do security-wise on your end before looking to your users. Specifically, an overwhelming majority of cyber breaches are due to user negligence.
To make your business as safe from scammers as it can be, teach employees and customers about these online safety practices:
- When working in public, don’t use an unsecured Wi-Fi network
- Never log into work accounts on a personal device
- Use strong passwords and enable user authentication when possible
- Constantly update your systems and antivirus software
The above list is by no means comprehensive. There are a number of other safety precautions that users should follow. Otherwise, your data won’t be as protected as you think it is.
Remember, not every security practice is in your control. However, if there is a data breach, all eyes will be on you, not your users. Beyond security tools, all you can do is educate employees and customers and hope for the best.
7. Ensure users know about cyber threats
Nonetheless, users may still encounter an attempted breach. There’s no limit to how far hackers will go to steal financial information.
When teaching your users about online safety, ensure they know about the different types of cyberattacks so they can avoid bank and payroll fraud. These include:
- Phishing. In a phishing attack, a cybercriminal entices recipients to open emails from a trusted entity. In this case, that trusted entity is your business. Once they click on a link within the email, your company’s data (including financial information) can be compromised.
- Malware. By hacking your sight and installing malware, unauthorized users can steal your data. Essentially, malware steals critical information, can insert pop-up ads on your site, and can even redirect your site to another webpage.
- Man-in-the-middle attack. In this attack, a hacker eavesdrops on and alters the communication between your site’s users and your business. Hackers usually do this by setting up a Wi-Fi connection with a similar name as a nearby business. Then, when a user connects to it, they can intercept their online communications.
- Distributed denial-of-service (DDoS) attack. Hackers attempt to overload your servers by submitting hundreds of requests from compromised IP addresses. This can slow down your website or even cause it to go offline temporarily. Cybercriminals distract businesses with DDoS attacks while they steal critical data on the network.
Regardless of your business’s size, you’re always prone to cyber threats. Make sure your employees and customers are educated on cyberattacks, so they don’t fall victim to them.
When it comes to protecting your financial information, you can never take too many precautions. From enabling password alternatives to educating users about cyber threats, there are innumerable security options. Remember to ensure that any software you leverage takes these security precautions as well.
Now that you know more about cybersecurity, don’t wait; start protecting your business’s financial information now.
These views are made solely by the author.



